Search for "tor" returned 10368 results
61 min
Attacking Rich Internet Applications
Not your mother's XSS bugs
63 min
Banking Malware 101
Overview of Current Keylogger Threats
66 min
La Quadrature du Net - Campaigning on Telecoms Package
Pan-european activism for patching a "pirated" law

52 min
Objects as Software: The Coming Revolution
How RepRap and physical compilers will change the world as…
56 min
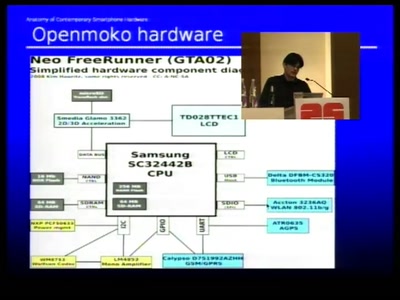
Anatomy of smartphone hardware
Dissecting contemporary cellphone hardware
58 min
Advanced memory forensics: The Cold Boot Attacks
Recovering keys and other secrets after power off
66 min
Cisco IOS attack and defense
The State of the Art

61 min
Handschellen hacken
Essentielles Grundwissen für alle, die nichts zu verbergen…
37 min
Cracking the MSP430 BSL
Part Two
23 min
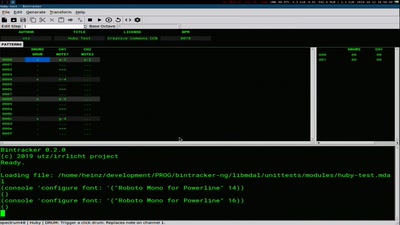
Bintracker
A chiptune audio workstation for the 21st century

25 min
GeoHealthCheck
Uptime and QoS monitor for geospatial web-services

58 min
Terraforming Planet Earth
Practical terraforming technologies for regenerating soils…
48 min
What is forensic software doing in journalism (and elsewhere)?
We have too much data: Watch. Suggest. Help.

33 min
Open source experimental incubator build up
call for participation in project and product development
45 min
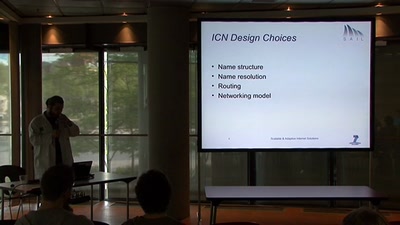
Information Centric Networking
A radically new paradigm for the future internet

56 min
Openmoko: 5 years after – What's left behind.
Free software and hardware projects for mobile communication
50 min
Wrangling Git
Git power tips for the intermediate Git user

37 min
Hacking (with) a TPM
Don't ask what you can do for TPMs, Ask what TPMs can do…
38 min
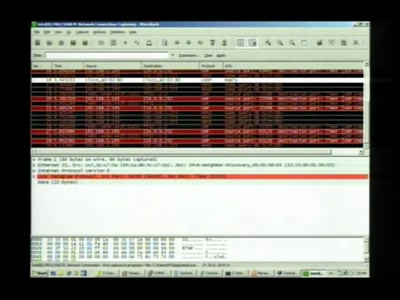
Squeezing Attack Traces
How to get useable information out of your honeypot
58 min
Collapsing the European security architecture
More security-critical behaviour in Europe!
63 min
Exploiting Symbian
Symbian Exploit and Shellcode Development

48 min
SWF and the Malware Tragedy
Hide and Seek in A. Flash
45 min