Search for "nook" returned 2118 results
58 min
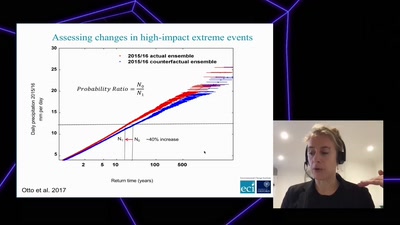
Angry weather ?
How human-induced climate change affects weather (& how we…
56 min
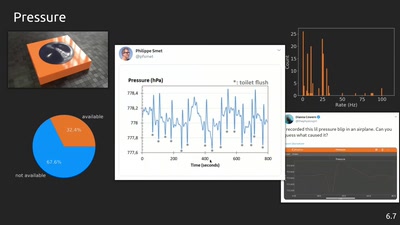
phyphox: Using smartphone sensors for physics experiments
An open source project for education, research and tinkering

55 min
The Gospel of IRMA
Attribute Based Credentials in Practice
60 min
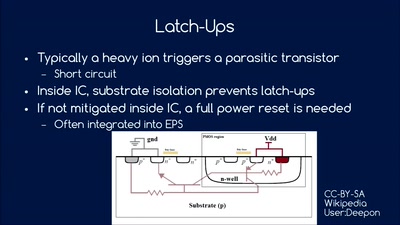
So you want to build a satellite?
How hard can it be? An introduction into CubeSat development
58 min
Script Your Car!
Using existing hardware platforms to integrate python into…

30 min
apertus° AXIOM
The first Open Source Cinema Camera
38 min
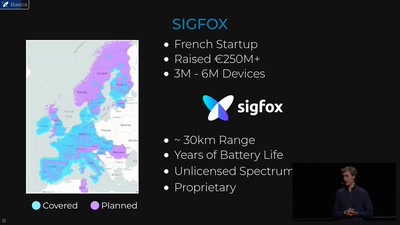
Hunting the Sigfox: Wireless IoT Network Security
Dissecting the radio protocol of Sigfox, the global…
45 min
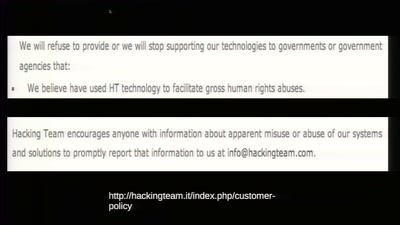
To Protect And Infect
The militarization of the Internet

63 min
Dissecting HDMI
Developing open, FPGA-based capture hardware for conference…
39 min
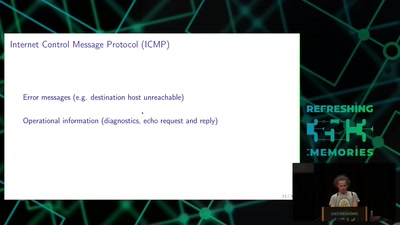
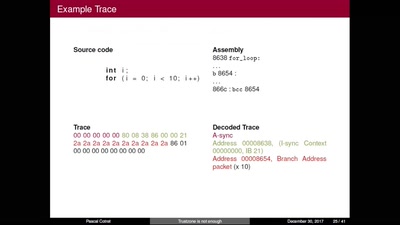
Transmission Control Protocol
TCP/IP basics
58 min
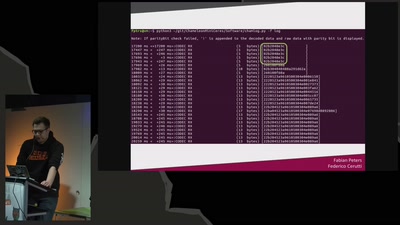
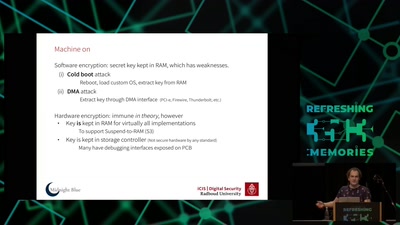
Self-encrypting deception
weaknesses in the encryption of solid state drives (SSDs)
55 min
ZombieLoad Attack
Leaking Your Recent Memory Operations on Intel CPUs
31 min