Search for "Hans de Raad" returned 1105 results
39 min
DISNOVATION.ORG
Disobedient Innovation
58 min
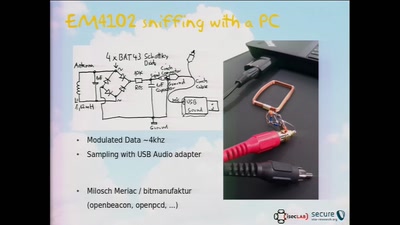
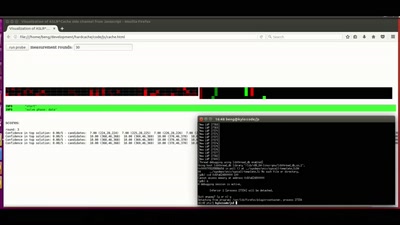
RFID Treehouse of Horror
Hacking City-Wide Access Control Systems

22 min
Trust us and our business will expand!
Net-activism strategies against fake web companies
60 min
Profiling (In)justice
Disaggregating Data by Race and Ethnicity to Curb…
61 min
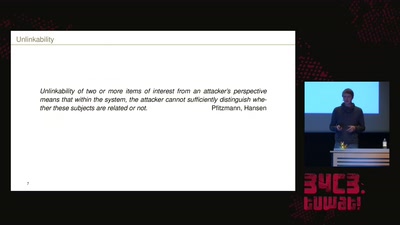
How Alice and Bob meet if they don't like onions
Survey of Network Anonymisation Techniques
60 min
Internet Cube
Let's Build together a Free, Neutral and Decentralized…
28 min
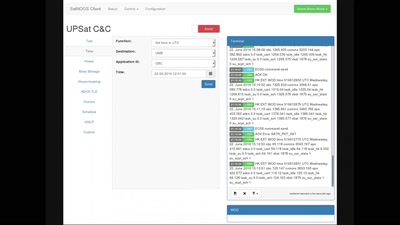
SatNOGS: Crowd-sourced satellite operations
Satellite Open Ground Station Network
51 min
The GNU Name System
A Decentralized PKI For Social Movements
41 min
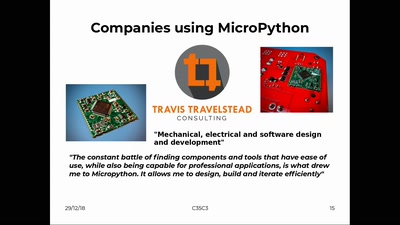
MicroPython – Python for Microcontrollers
How high-level scripting languages make your hardware…

32 min
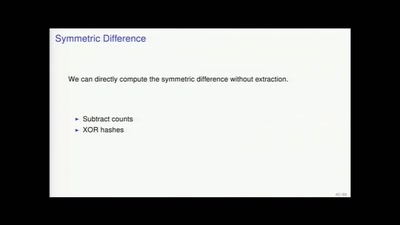
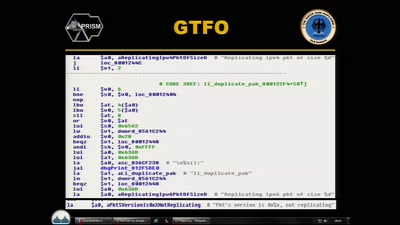
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
64 min
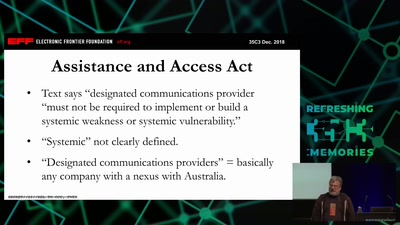
It Always Feels Like the Five Eyes Are Watching You
Five Eyes’ Quest For Security Has Given Us Widespread…
55 min
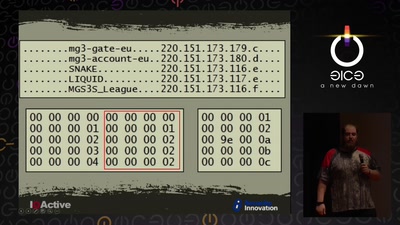
Cyber Necromancy
Reverse Engineering Dead Protocols
46 min
CounterStrike
Lawful Interception
38 min
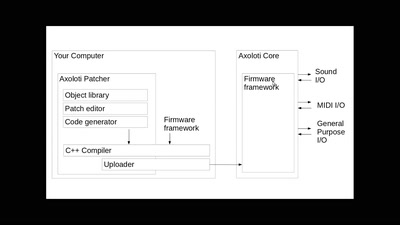
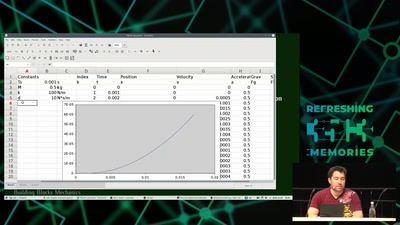
Modeling and Simulation of Physical Systems for Hobbyists
Essential Tools for Developing, Testing and Debugging…
44 min