Search for "36c3" returned 2559 results
60 min
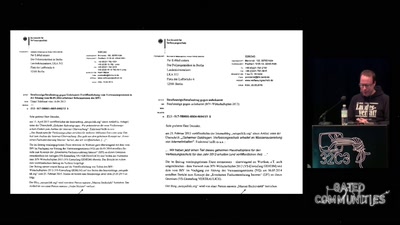
Ein Abgrund von Landesverrat
Wie es dazu kam und was daraus zu lernen ist
60 min
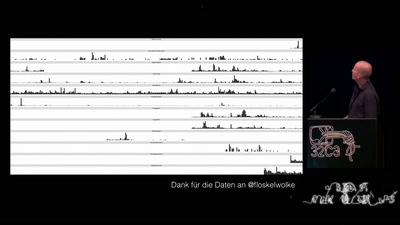
„Nach bestem Wissen und Gewissen“ – Floskeln in der Politik
Politische Phrasologie – warum man aus dem ganzen Zeug, das…
33 min
Kampf dem Abmahnunwesen
Wider die automatisierte Rechtsdurchsetzung
59 min
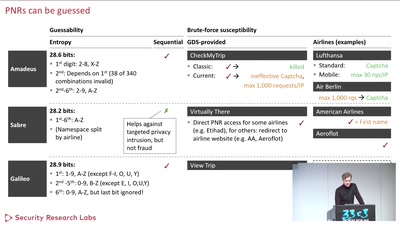
Where in the World Is Carmen Sandiego?
Becoming a secret travel agent
57 min
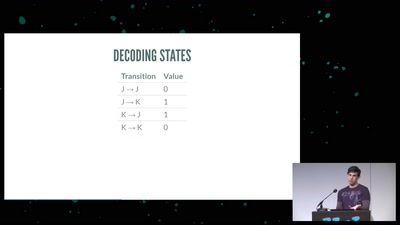
No USB? No problem.
How to write an open source bit-bang low-speed USB stack…
60 min
A Story of Discrimination and Unfairness
Prejudice in Word Embeddings
42 min
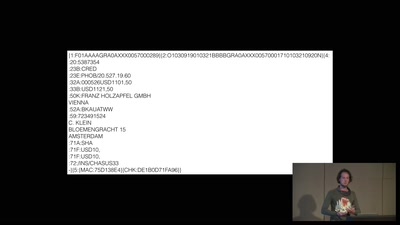
A world without blockchain
How (inter)national money transfers works

60 min
What does Big Brother see, while he is watching?
Uncovering images from the secret Stasi archives.

61 min
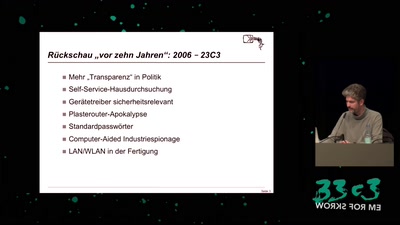
Ten years after ‚We Lost The War‘
The future does not look much brighter than ten years ago.…
59 min
The Ultimate SPC700 Talk
The hardware behind the music of Super Mario World, Chrono…
41 min
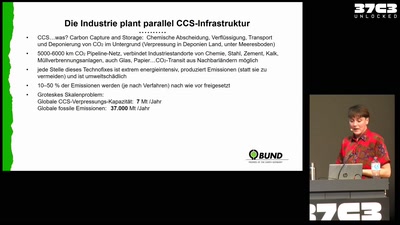
Blackbox Chemieindustrie
Die energieintensivste Industrie Deutschlands
39 min
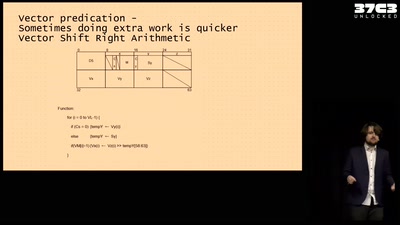
Making homebrew for your very own Vector Super Computer
Adventures running a NEC Vector Engine for fun and ...…
38 min
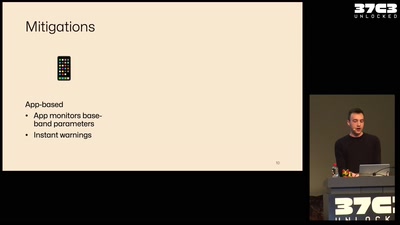
What your phone won’t tell you
Uncovering fake base stations on iOS devices
61 min
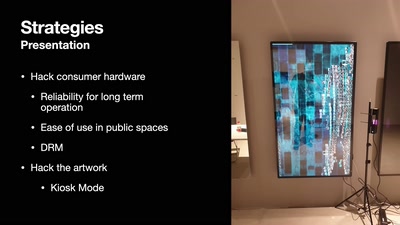
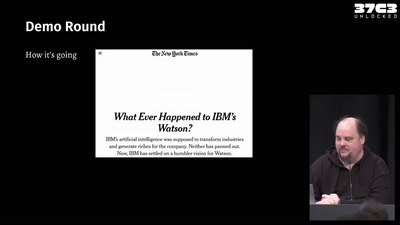
DevOps but for artworks in museums
A look into pipelines ending in museums and not in the cloud
46 min
Writing secure software
using my blog as example

61 min
How Many Planets in Our Solar System? Glad You Asked!
How Astronomy Knew 6 Planets, Then Found 20 More, Then Went…
56 min
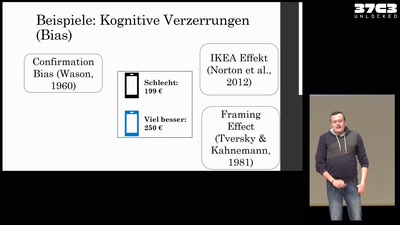
Social Engineering: Geschichte, Wirkung & Maßnahmen.
Alles, was ihr immer über Social Engineering wissen…
42 min
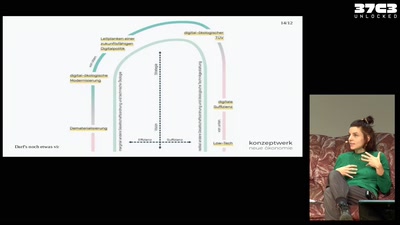
Darf's noch etwas visionärer sein?
Digital-ökologische Zukunftsvorstellungen in der…
61 min