Search for "Lia Strenge"
prev
next
26 min
How technology is used to subvert and circumvent…
54 min
Do you care about Matroshka processors?
49 min
How to turn your KVM into a raging key-logging monster
60 min
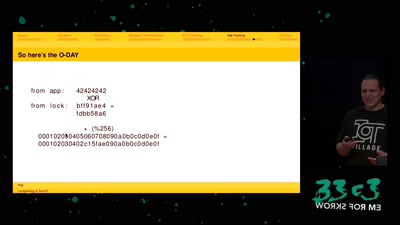
...or why adding BTLE to a device sometimes isn't smart at…
46 min
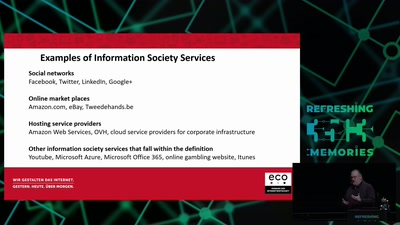
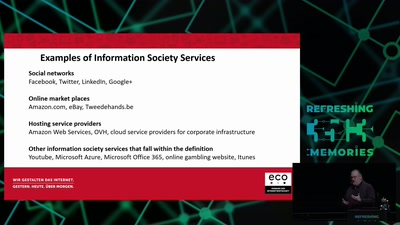
An introduction and critique of the EC proposal for a…
59 min
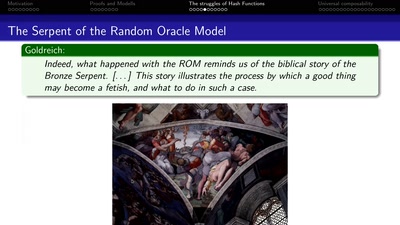
How I learned to stop worrying and love the backdoor
49 min
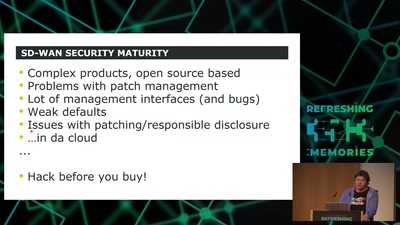
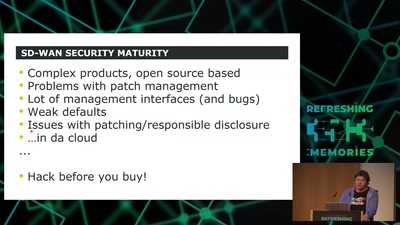
How to hack software defined network and keep your sanity?
63 min
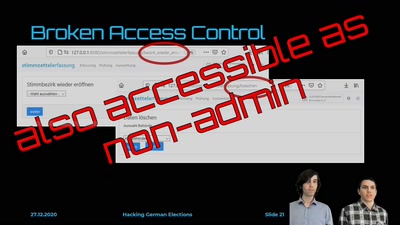
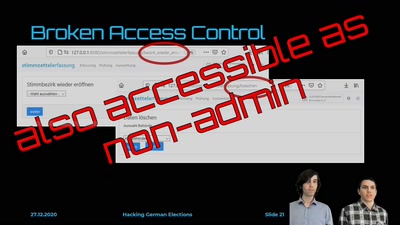
Insecure Electronic Vote Counting - How It Returned and Why…
58 min
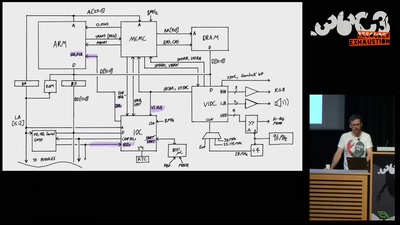
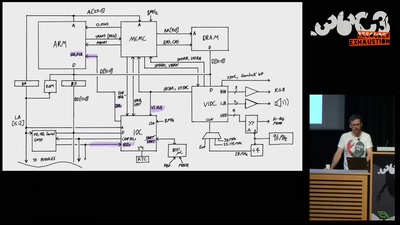
Everything about the Archimedes computer (with zero…
30 min
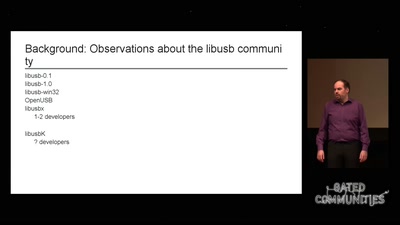
How I failed to run an open source project
71 min
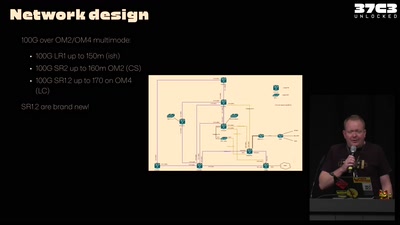
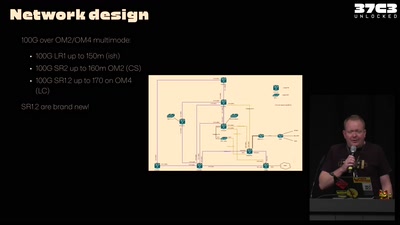
Teams presenting how they helped making this awesome event
32 min
Approaches to working with sound and network data…
61 min
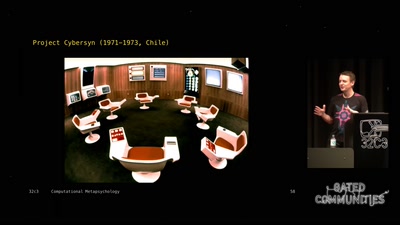
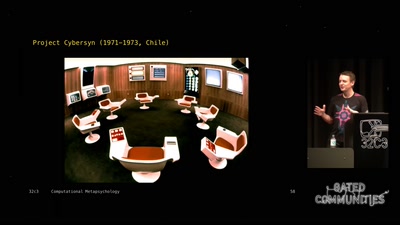
An Artificial Intelligence exploration into the creation of…
39 min
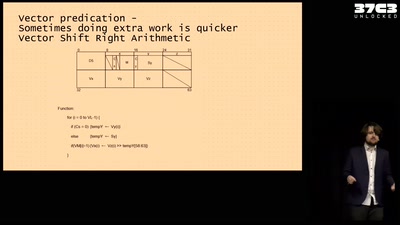
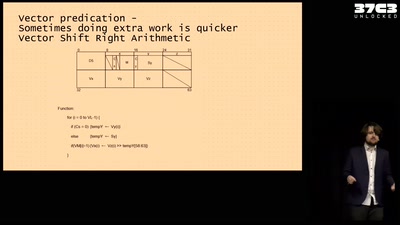
Adventures running a NEC Vector Engine for fun and ...…
30 min
Visualizing WLAN Channel Usage on OpenWRT
prev
next