Search for "Jums"
prev
next
57 min
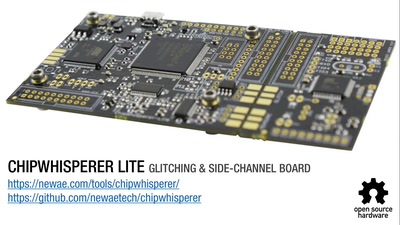
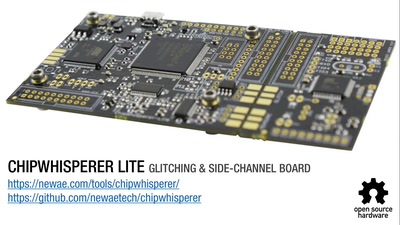
Hardware attacks on the latest generation of ARM Cortex-M…
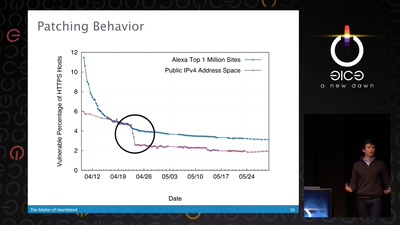
50 min
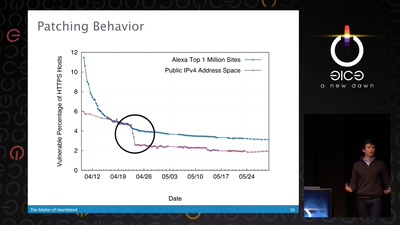
What went wrong, how the Internet reacted, what we can…
29 min
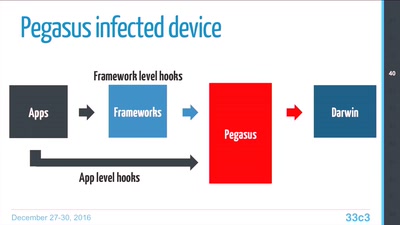
Technical Teardown of the Pegasus malware and Trident…
42 min
Embedded Security Using Binary Autotomy
42 min
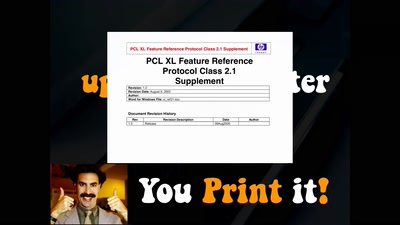
Your princess is AES encrypted in another castle
63 min
What you need and how it works. An experiences report

61 min
How Astronomy Knew 6 Planets, Then Found 20 More, Then Went…
38 min
Aarch64 binary rewriting adventures but mostly pains
64 min
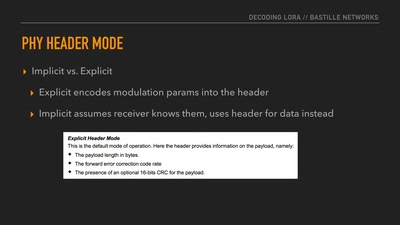
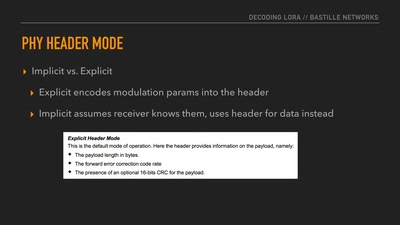
Dissecting a Modern Wireless Network for the Internet of…
58 min
From the Outside Looking In
41 min
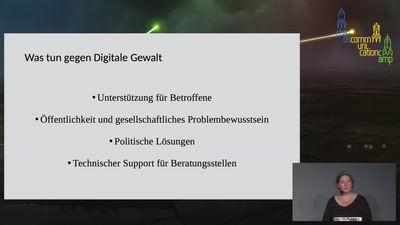
"Nicht dem Phänomen Cybercrime im engeren Sinne zuzuordnen"…
60 min
'Liberating' Firmware from Closed Devices with Open Source…
46 min
Hacking your network likes it's 1980 again
prev
next