Search for "Bruce Dang"
prev
42 min
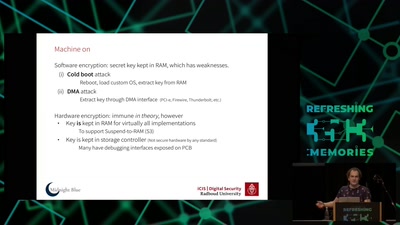
Your princess is AES encrypted in another castle
63 min
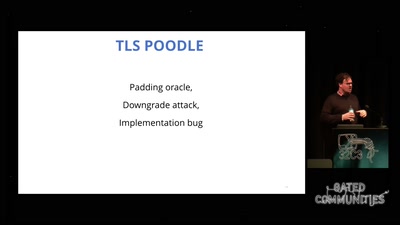
exploring two decades of transport layer insecurity
63 min
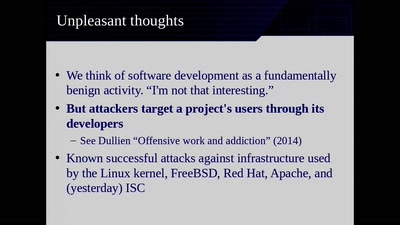
Moving Beyond Single Points of Failure for Software…
61 min
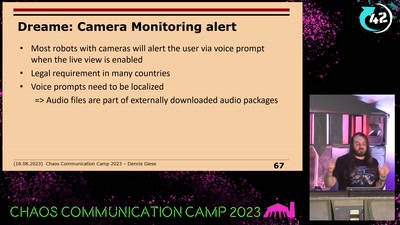
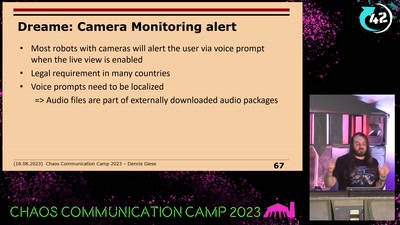
prevent your robot from sucking your data
57 min
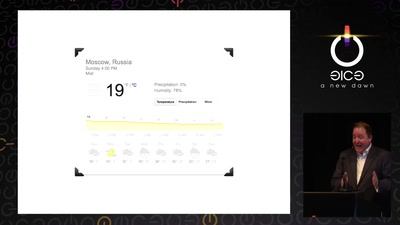
Turbulence, Big Data, AI, Fake News, and Peak Knowledge
60 min
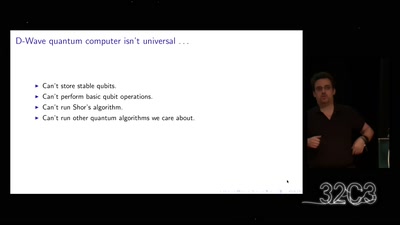
A gentle introduction to post-quantum cryptography
58 min
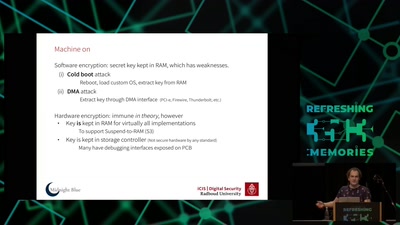
weaknesses in the encryption of solid state drives (SSDs)
55 min
The story of the NSA listening post – told by an ex-SIGINT…

59 min
The future of IC analysis
prev