Search for "ssh" returned 720 results

32 min
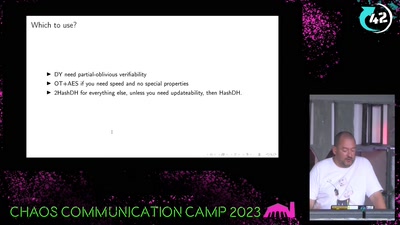
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
59 min
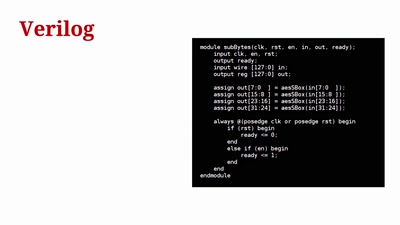
Towards General Purpose Reconfigurable Computing on Novena
FPGAs for Everybody with Novena
58 min
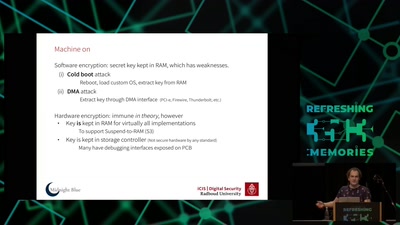
Self-encrypting deception
weaknesses in the encryption of solid state drives (SSDs)
48 min
10 Years of Fun with Embedded Devices
How OpenWrt evolved from a WRT54G firmware to an universal…
54 min
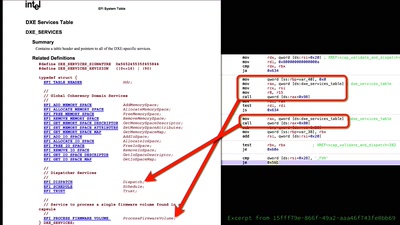
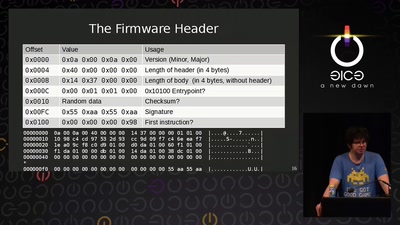
AMD x86 SMU firmware analysis
Do you care about Matroshka processors?
60 min
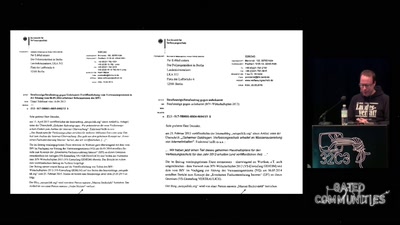
Ein Abgrund von Landesverrat
Wie es dazu kam und was daraus zu lernen ist
43 min
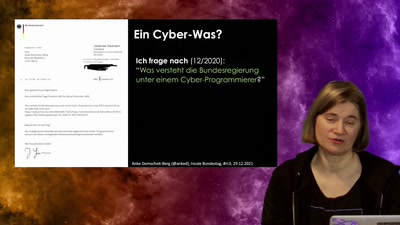
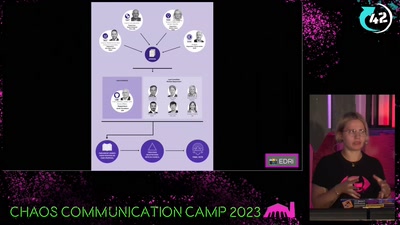
Chat-Control
now is the time to take action!

59 min
Security of the IC Backside
The future of IC analysis
59 min
Fernvale: An Open Hardware and Software Platform, Based on the (nominally) Closed-Source…
A Lawful Method for Converting Closed IP into Open IP
64 min
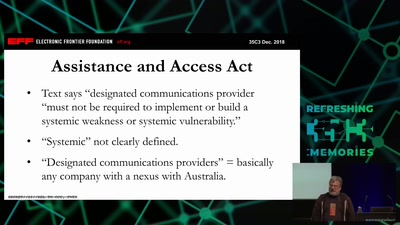
It Always Feels Like the Five Eyes Are Watching You
Five Eyes’ Quest For Security Has Given Us Widespread…
61 min
Now I sprinkle thee with crypto dust
Internet reengineering session
60 min
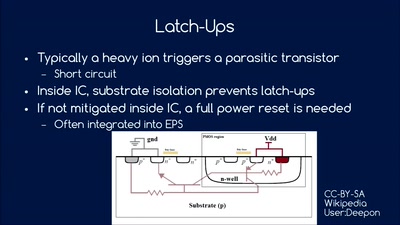
So you want to build a satellite?
How hard can it be? An introduction into CubeSat development

58 min
Operation Triangulation
What You Get When Attack iPhones of Researchers
128 min
Methodisch inkorrekt!
Die Wissenschaftsgala vom 32C3
95 min
Hacker Jeopardy
Zahlenraten für Geeks
60 min
Check your privileges!
How to drop more of your privileges to reduce attack…
58 min