Search for "36c3" returned 2559 results
38 min
Unpacking the compromises of Aadhaar, and other digital identities inspired by it
Governments around the world are implementing digital…

63 min
The Case Against WikiLeaks: a direct threat to our community
How to understand this historic challenge and what we can…
63 min
Human Rights at a Global Crossroads
Whistleblowers and the Cases of The Snowden Refugees and…
41 min
Extinction Rebellion
Jahresrückblick 2019
40 min
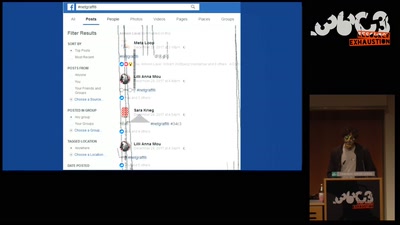
Art against Facebook
Graffiti in the ruins of the feed and the…
38 min
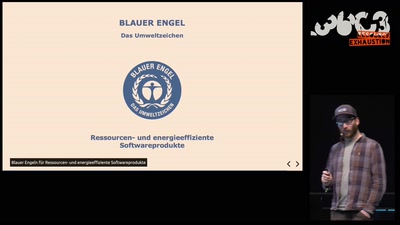
The Planet Friendly Web
Warum unser Web nachhaltiger werden muss und wie wir das…
62 min
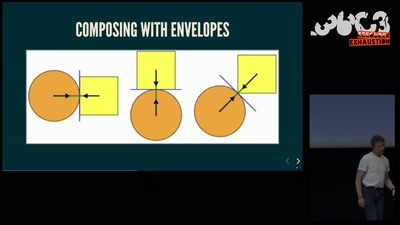
Getting software right with properties, generated tests, and proofs
Evolve your hack into robust software!
46 min
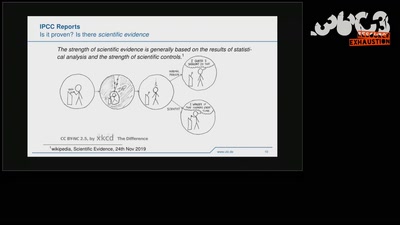
Climate Modelling
The Science Behind Climate Reports
91 min
What the World can learn from Hongkong
From Unanimity to Anonymity
58 min
Hack_Curio
Decoding The Cultures of Hacking One Video at a Time

115 min
Hacker Jeopardy
Zahlenraten für Geeks
60 min
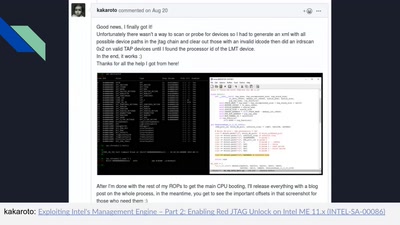
Intel Management Engine deep dive
Understanding the ME at the OS and hardware level
55 min