Search for "Jack Random"
prev
next

45 min
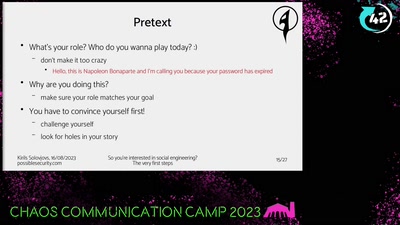
Spotting (digital) tech fictions as replacement for social…
61 min
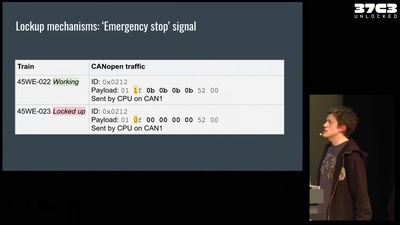
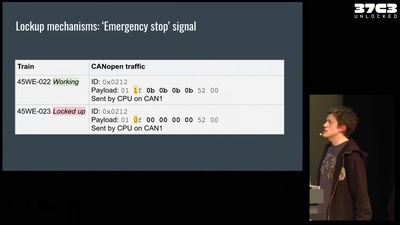
Reverse engineering a train to analyze a suspicious…

60 min
Efail, other attacks and lessons learned.
42 min
Your princess is AES encrypted in another castle

57 min
An introduction into reverse-engineering x86 microcode and…

61 min
How Astronomy Knew 6 Planets, Then Found 20 More, Then Went…
54 min
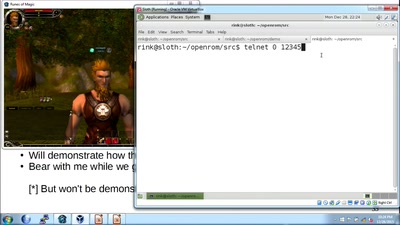
An introduction to reverse engineering network protocols
59 min
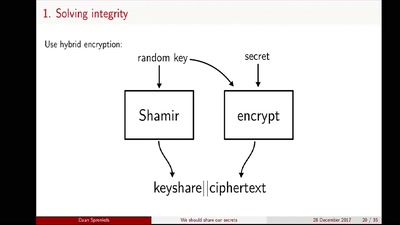
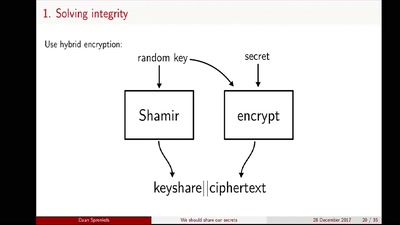
Shamir secret sharing: How it works and how to implement it
59 min
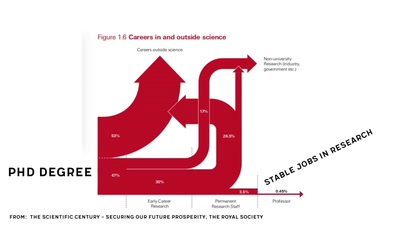
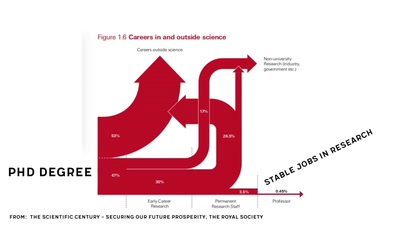
Let's understand how the scientific system works

45 min
the first three years of a six month project.
62 min
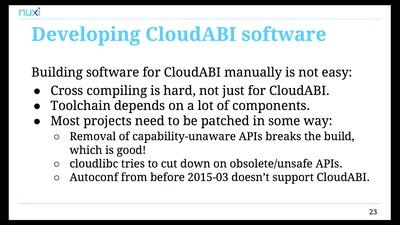
Pure capability-based security for UNIX
prev
next