Search for "Ben H." returned 6003 results
43 min
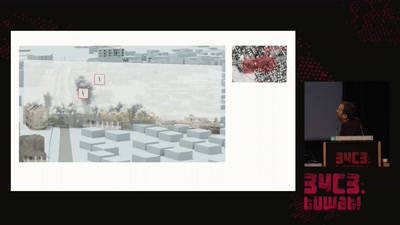
Forensic Architecture
Forensic Architecture is an independent research agency…
38 min
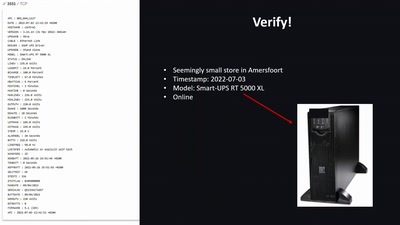
Honey, let's hack the kitchen:
Attacks on critical and not-so-critical cyber physical…
57 min
A New Dark Age
Turbulence, Big Data, AI, Fake News, and Peak Knowledge
39 min
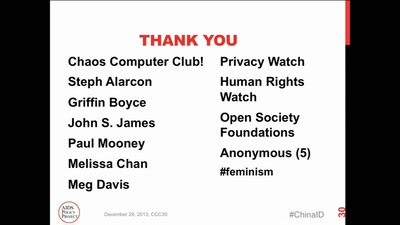
ID Cards in China: Your Worst Nightmare
In China Your ID Card Knows Everything
60 min
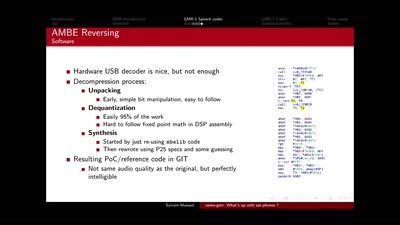
osmo-gmr: What's up with sat-phones ?
Piecing together the missing bits

64 min
Cory Doctorow – Fireside Chat
Reading and Q&A
60 min
Beyond your cable modem
How not to do DOCSIS networks
64 min
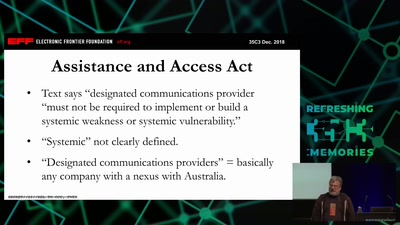
It Always Feels Like the Five Eyes Are Watching You
Five Eyes’ Quest For Security Has Given Us Widespread…
47 min
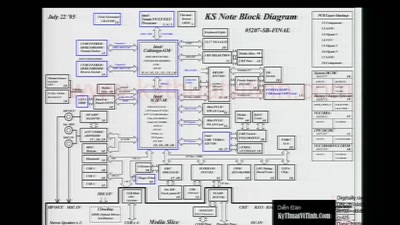
Hardening hardware and choosing a #goodBIOS
Clean boot every boot - rejecting persistence of malicious…
51 min
Virtual Secure Boot
Secure Boot support in qemu, kvm and ovmf.
56 min
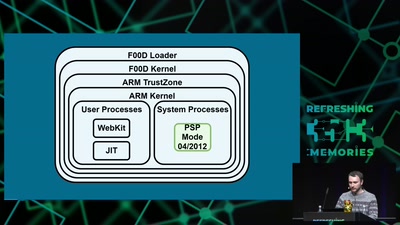
Viva la Vita Vida
Hacking the most secure handheld console
58 min
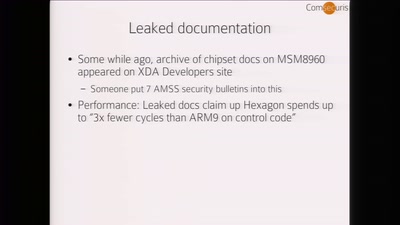
Baseband Exploitation in 2013
Hexagon challenges
33 min
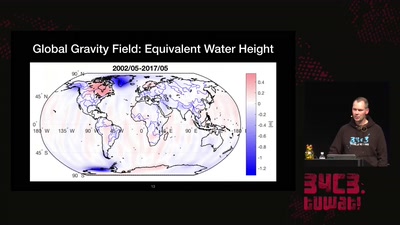
Watching the changing Earth
warning: gravity ahead
30 min
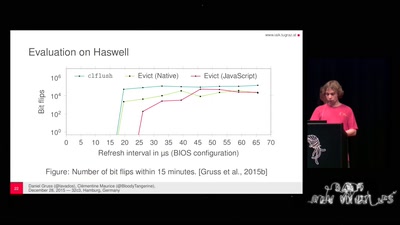
Rowhammer.js: Root privileges for web apps?
A tale of fault attacks on DRAM and attacks on CPU caches
56 min
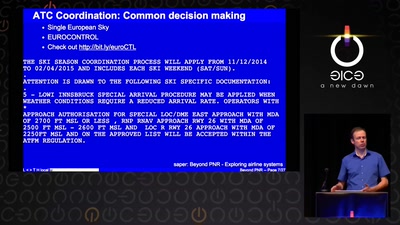
Planes and Ships and Saving Lives
How soft and hardware can play a key role in saving lives…

62 min