29 min
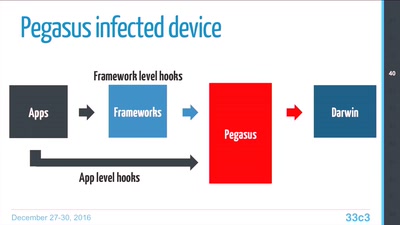
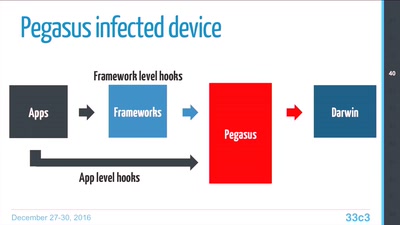
Technical Teardown of the Pegasus malware and Trident…
30 min
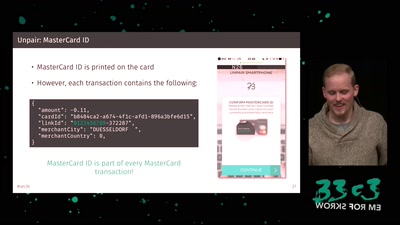
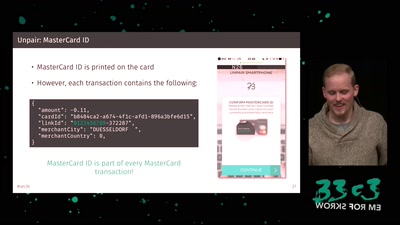
The Red Pill of N26 Security

33 min
Intrusion and Exfiltration in Server-less Architectures
36 min
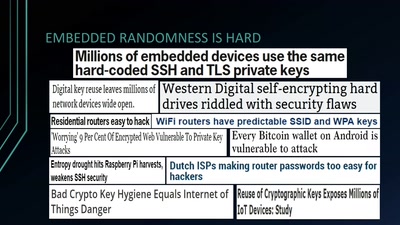
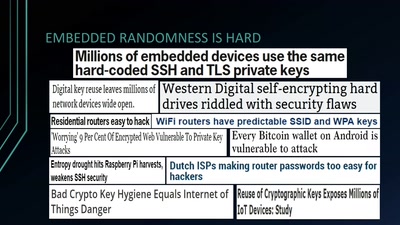
Analyzing Embedded OS Random Number Generators
37 min
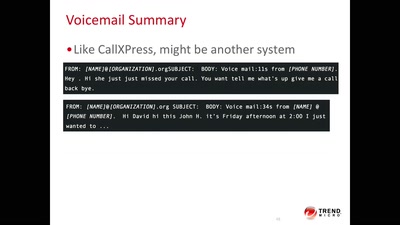
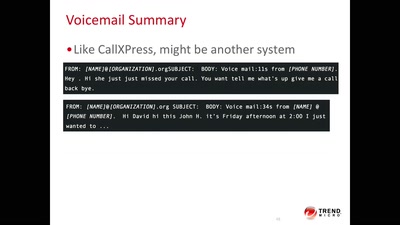
A systemic update of sensitive information that you sniff…
40 min
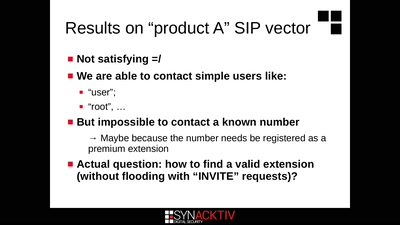
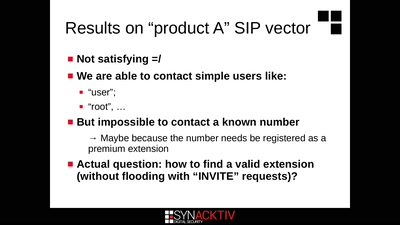
Call the frontdoor to install your backdoors
44 min
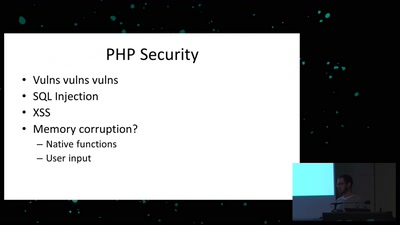
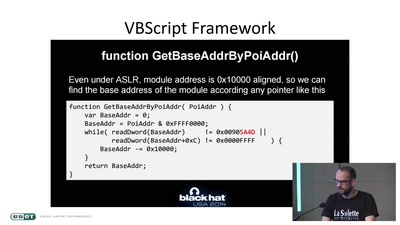
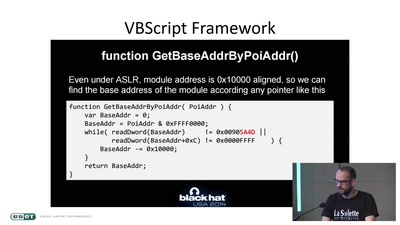
teaching a new dog old tricks
46 min
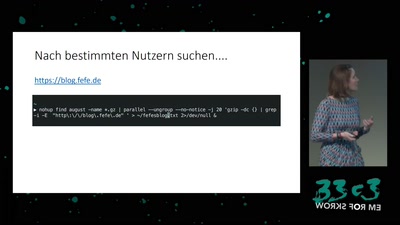
Finding interesting targets in 128bit of entropy
51 min
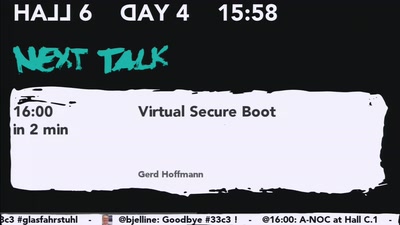
Secure Boot support in qemu, kvm and ovmf.
55 min
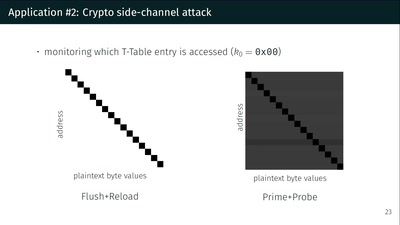
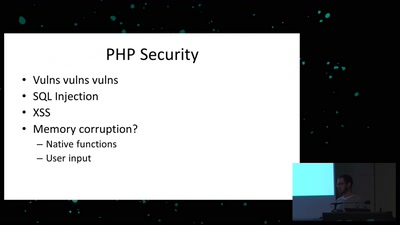
Side effects include side-channel attacks and bypassing…
59 min
A Journey in the Land of (Cyber-)Espionage
59 min
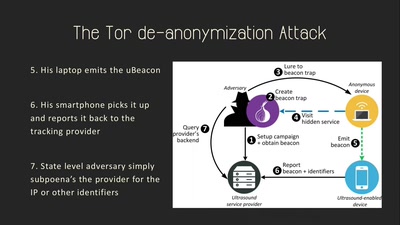
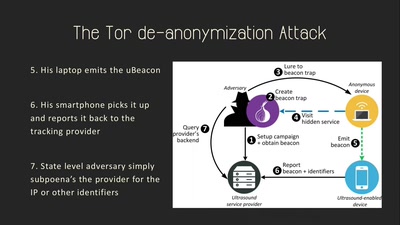
On the Privacy & Security of the Ultrasound Tracking…
59 min
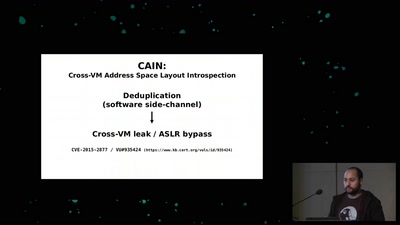
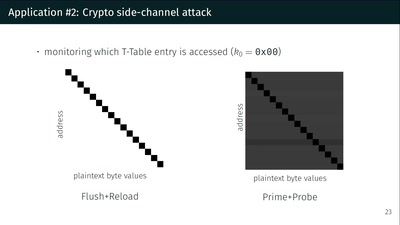
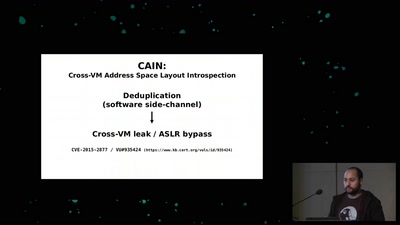
A tale of 3 different memory deduplication based…
59 min
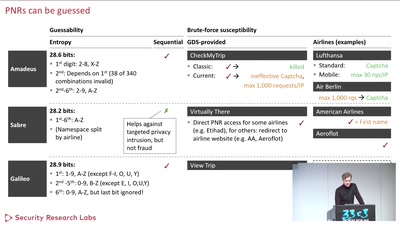
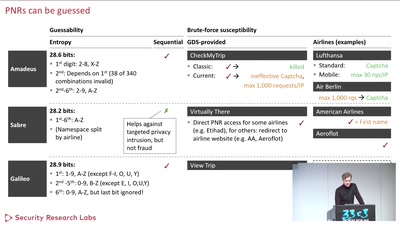
Becoming a secret travel agent
60 min
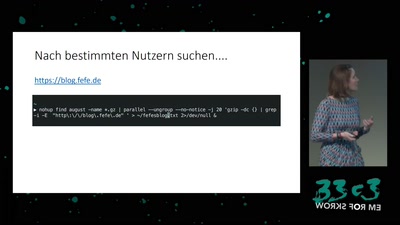
How private companies leak your personal data into the…
61 min
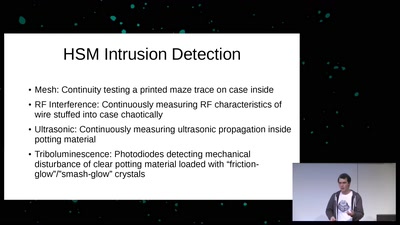
A proposal for secure computing in an age where we cannot…

61 min
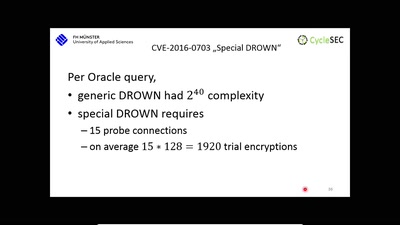
Improving the encrypted the web, one round-trip at a time
63 min
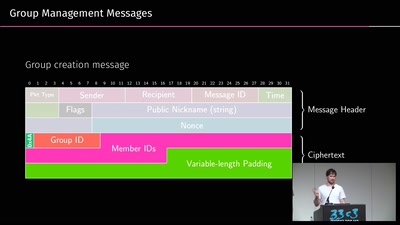
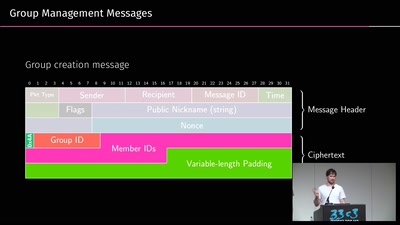
A gentle introduction to mobile messaging and subsequent…
64 min
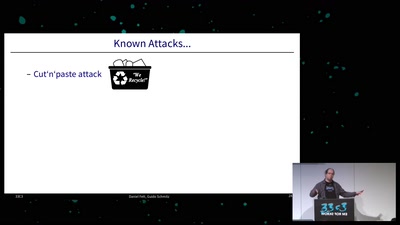
(Not Only) Attacks on OAuth and OpenID Connect
64 min
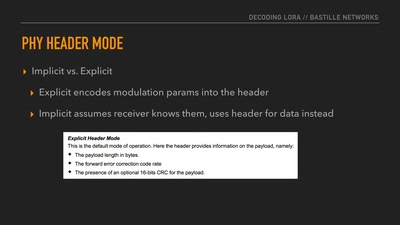
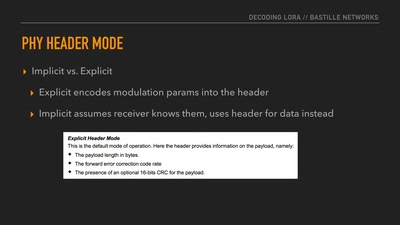
Dissecting a Modern Wireless Network for the Internet of…