85 min
Fnord-Jahresrückblick
Diesmal mit noch mehr Eurozonen-Spaltung!
162 min
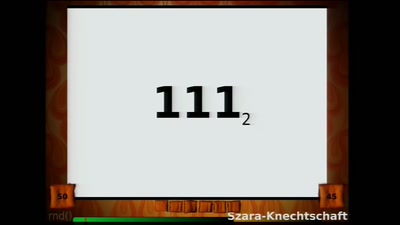
Hacker Jeopardy
Zahlenraten für Geeks
59 min
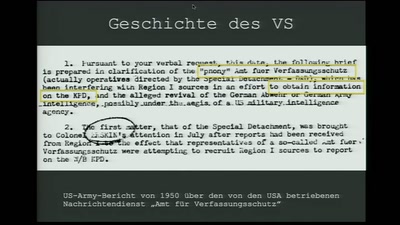
Best of ... Verfassungsschutz
Der Verfassungsschutz schützt die Verfassung so wie…
54 min
Hacking Cisco Phones
Just because you are paranoid doesn't mean your phone isn't…
83 min
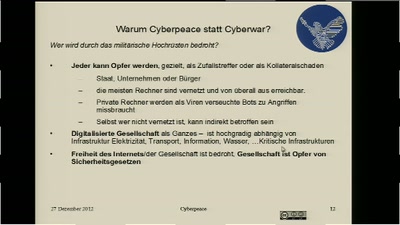
Security Nightmares
Damit Sie auch morgen schlecht von Ihrem Computer träumen.
48 min
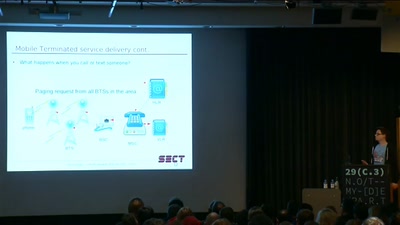
Let Me Answer That for You
adventures in mobile paging
45 min
Further hacks on the Calypso platform
or how to turn a phone into a BTS
51 min
The ultimate Galaksija talk
Everything about a Yugoslavian microcomputer halfway…
59 min
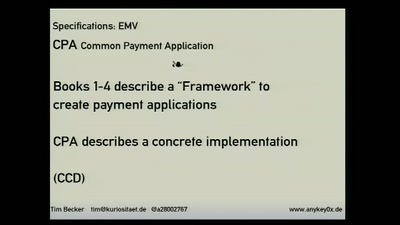
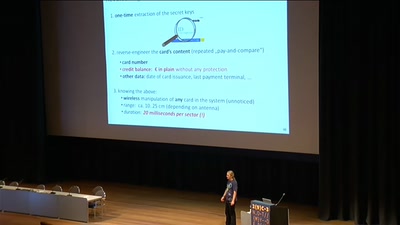
Milking the Digital Cash Cow
Extracting Secret Keys of Contactless Smartcards
57 min
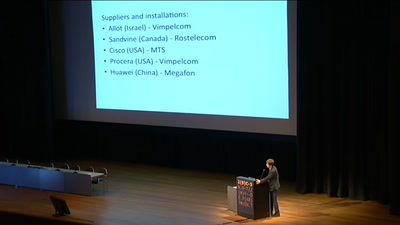
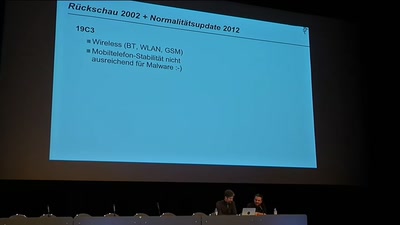
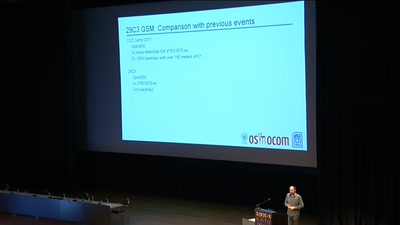
29C3 GSM: Cell phone network review
262 42 - The full spectrum
51 min
Open Source Schlüssel und Schlösser
Offene Quellen zum Bösen und Guten: von downloadbaren…
138 min
Enemies of the State: What Happens When Telling the Truth about Secret US Government…
Blowing the Whistle on Spying, Lying & Illegalities in the…
56 min
SCADA Strangelove
or: How I Learned to Start Worrying and Love Nuclear Plants

59 min
Netzaktivisten! Ist das alles, was wir drauf haben?
Eine subjektive Bestandsaufnahme

63 min
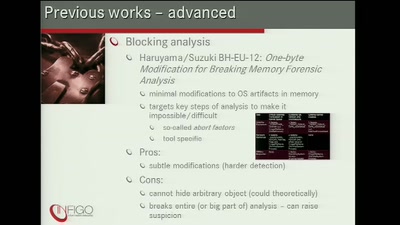
Writing a Thumbdrive from Scratch
Prototyping Active Disk Antiforensics
89 min
Nougatbytes 10
Gebilde(r)ter Hirnsalat – die rhekkcüЯ der Bilderrätsel
49 min
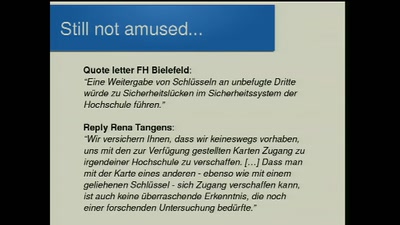
Men who stare at bits
RFID-Studierendenkarten mit Fehlern
61 min
Hackers As A High-Risk Population
Harm Reduction Methodology

45 min
Hanussen's mindreading
Experiments of the historical psychic
59 min
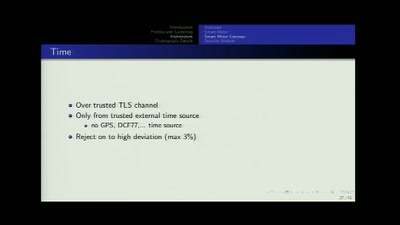
SmartMeter
A technological overview of the German roll-out
55 min
"How I met your pointer"
Hijacking client software for fuzz and profit
57 min
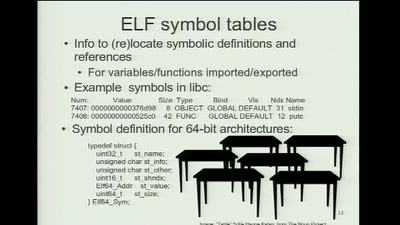
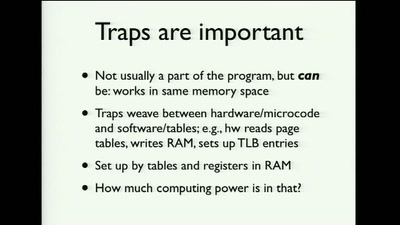
Page Fault Liberation Army or Gained in Translation
a history of creative x86 virtual memory uses
27 min
Romantic Hackers
Keats, Wordsworth and Total Surveillance
59 min
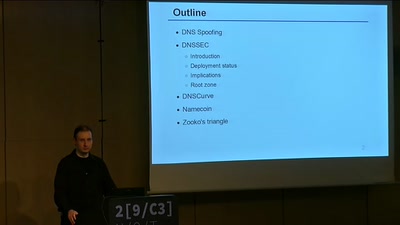
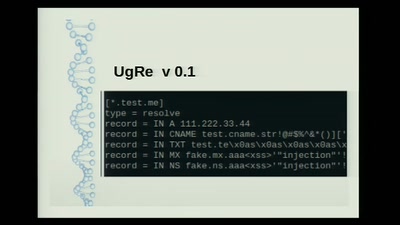
An Overview of Secure Name Resolution
DNSSEC, DNSCurve and Namecoin
71 min
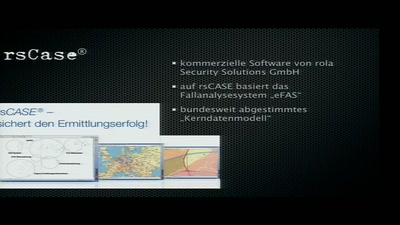
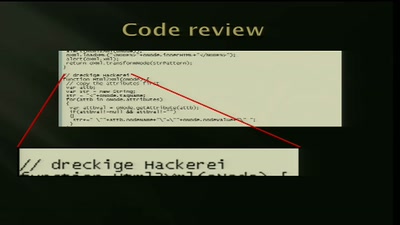
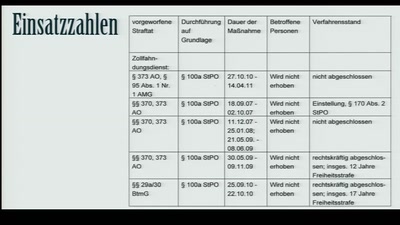
Trojaner-Blindflug
Spionage-Software von Staats wegen
58 min
Hacking Philosophy
Digitale Mündigkeit, Technikpaternalismus und warum wir…
58 min
Meine Kleidung funkt
Tracking von Menschen durch in Kleidung integrierte…
59 min
Security Evaluation of Russian GOST Cipher
Survey of All Known Attacks on Russian Government…
49 min
Safecast: DIY and citizen-sensing of radiation
Empowering citizen in the wake of Fukushima triple-meltdown…
59 min
Der Mord fällt aus
Ein Werkstattbericht der GEMA-Alternative C3S
59 min
Meldegesetz
Was aus dem 57-Sekunden-Gesetz wurde
38 min
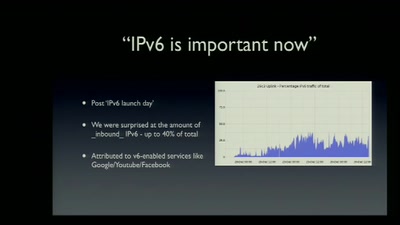
NOC Review
NOC Review about the 29C3
54 min
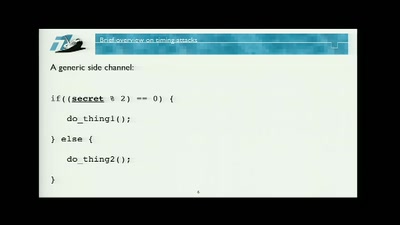
Time is NOT on your Side
Mitigating Timing Side Channels on the Web
45 min
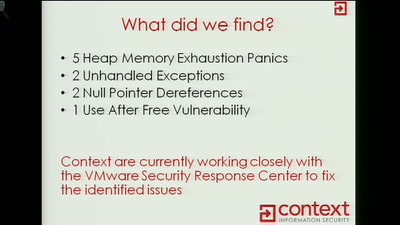
ESXi Beast
Exploiting VMWARE ESXi Binary Protocols Using CANAPE
23 min
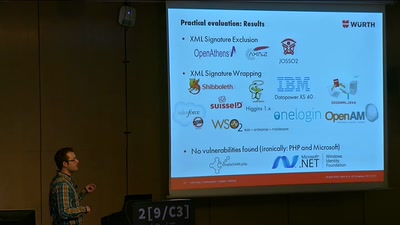
On Breaking SAML
Be Whoever You Want to Be
63 min
chmod o+rw bundestag
Mehr Transparenz und Teilhabe im Gesetzgebungsprozess

60 min
Pflanzenhacken richtig
Einblicke in die Weizenzüchtung
63 min
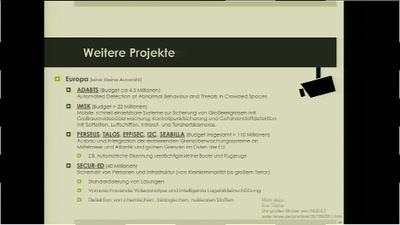
INDECT, Verhaltenserkennung & Co
automatisierte staatliche Verdächtigung
40 min
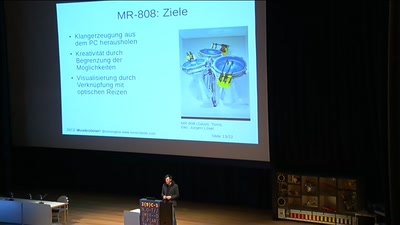
Marvin und der Blues
Wie Roboterinstrumente zum Musik machen benutzt werden…
51 min
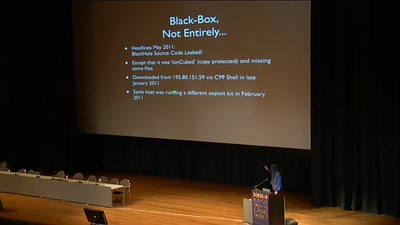
Analytical Summary of the BlackHole Exploit Kit
Almost Everything You Ever Wanted To Know About The…
68 min
The future of protocol reversing and simulation applied on ZeroAccess botnet
Mapping your enemy Botnet with Netzob
52 min
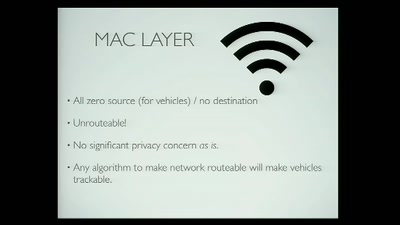
Privacy and the Car of the Future
Considerations for the Connected Vehicle

55 min
Zur Lage der Information
1.5 Jahre FragDenStaat.de
163 min
Lightning Talks 3
5 Minutes of Fame
58 min
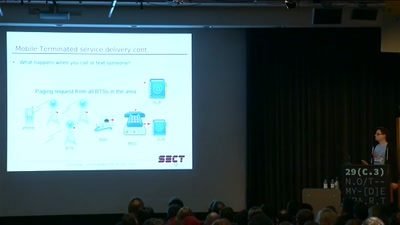
Setting mobile phones free
An overview of a mobile telephony market and how a…
61 min
Certificate Authority Collapse
Will the EU Succeed in Regulating HTTPS?
59 min
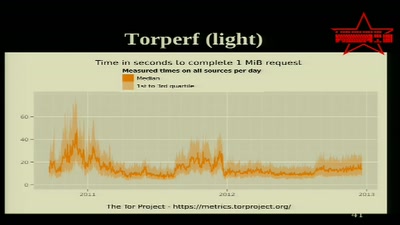
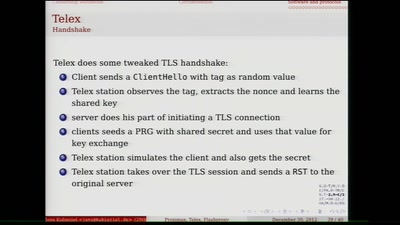
Proximax, Telex, Flashproxy oder Tor Bridges
Übersicht über aktuelle Zensurumgehungssoftware

126 min
Lightning Talks 1
5 Minutes of Fame
45 min
New Human Interfaces for Music
DIY MIDI Controllers
45 min
Sharing Access – Risiken beim Betrieb offener (WLAN-)Netze
Stand gestern, heute und morgen
47 min
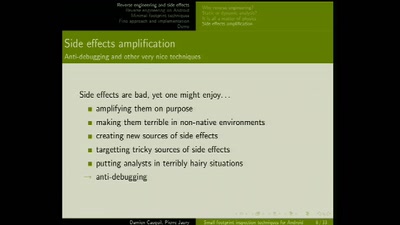
Small footprint inspection techniques for Android
Reverse engineering on Android platforms

60 min
The Grand EU Data Protection Reform
A latest battle report by some key actors from Brussels
61 min
Defend your Freedoms Online: It's Political, Stupid!
A Positive agenda against the next ACTA, SOPA, and such
146 min
Lightning Talks 2
5 Minutes of Fame
46 min
The Ethics of Activist DDOS Actions
A Historical Analysis

60 min
Privatisierung der Rechtsdurchsetzung
Von ACTA, IPRED und Freunden
48 min
Let Me Answer That for You
adventures in mobile paging
59 min
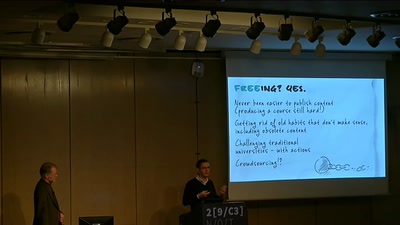
Millions of Lessons Learned on Electronic Napkins
On the way to free(ing) education
56 min
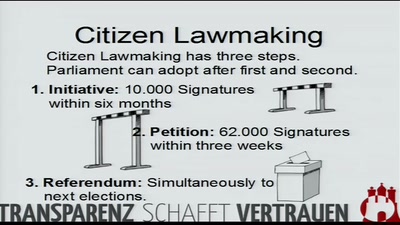
We are all lawmakers!
How to further transparency by law – the Hamburg example…
55 min
Our daily job: hacking the law
The key elements of policy hacking
42 min
IFG: Chance oder Bürgerbluff?
Informationsfreiheit in Deutschland. Ein Sachstand.
52 min
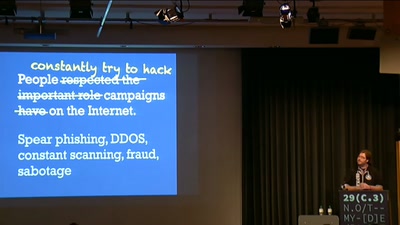
Securing the Campaign
Security and the 2012 US Presidential Election
54 min