Search for "sECuRE"
next
57 min
Why developing Secure Software is like playing Marble…
51 min
Secure Boot support in qemu, kvm and ovmf.
46 min
Suppression of secure communications by governments

61 min
fun(ctional) operating system and security protocol…
52 min
Who is the root on your router?
53 min
What the European Union wants. What the hackerdom can do..
45 min
Techniques and best practices to securely code your network…
50 min
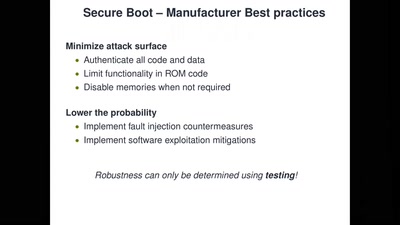
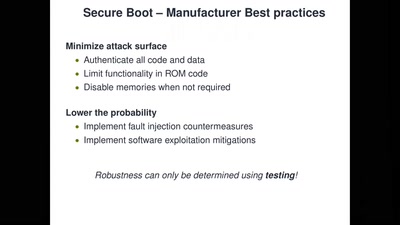
Bypassing Secure Boot using Fault Injection
57 min
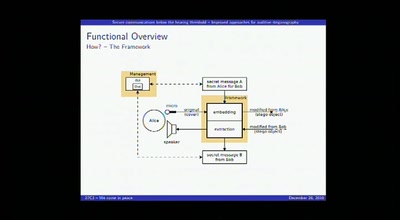
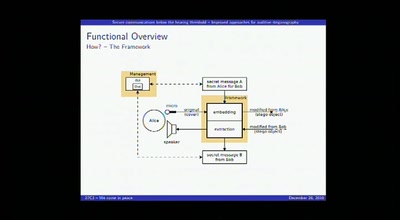
Improved approaches for auditive steganography
41 min
Security Of Railway Communication Protocols
next