Search for "guide"
next
49 min
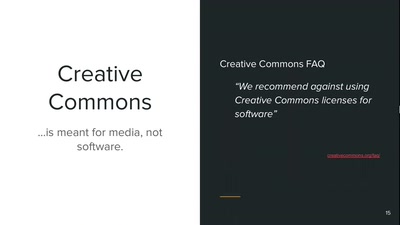
A talk about using free, open source licenses in everyday…
57 min
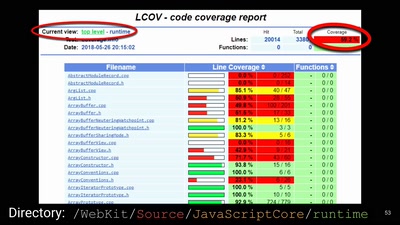
A demystification of the exploit development lifecycle
62 min
Creating Internet Privacy and Security Resources That Don't…
62 min
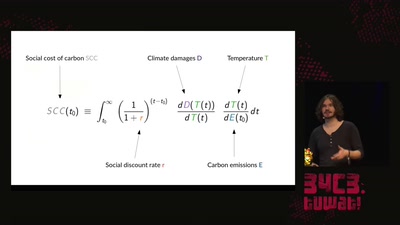
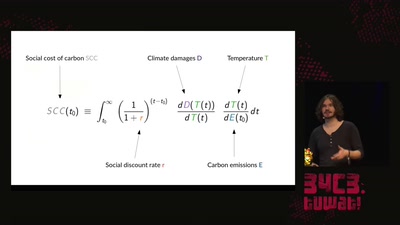
An introduction to the basics of climate research and what…

64 min
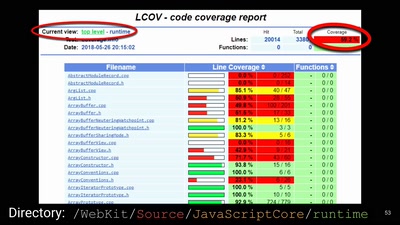
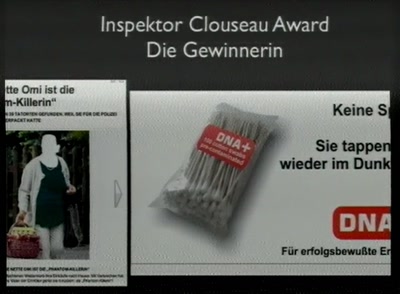
An investigation into intransparency
28 min
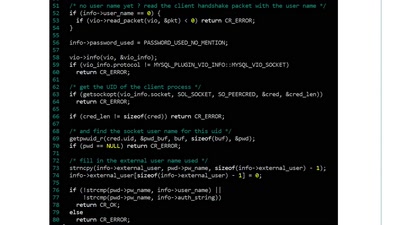
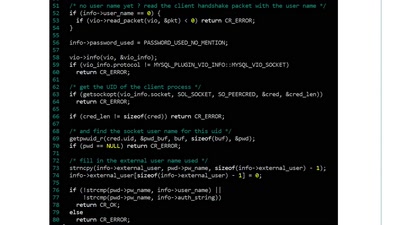
Hack on the MySQL code for fun and profit !
79 min
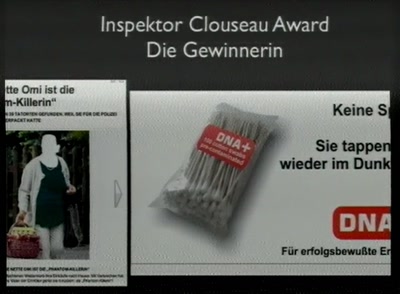
German / English version of the Fnord-Jahresrückblick 2009.
next