Search for "csk"
next
26 min
A new approach of identifying vulnerable web applications

54 min
A look at the upcoming standards by W3C

41 min
How to make use of democratic elections for your own purpose

57 min
An introduction into reverse-engineering x86 microcode and…

49 min
Introduction to syscall proxying and applications for in…
26 min
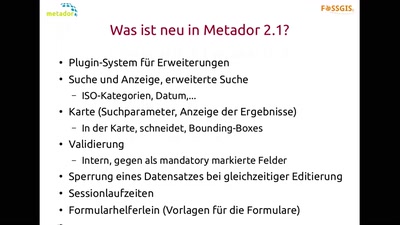
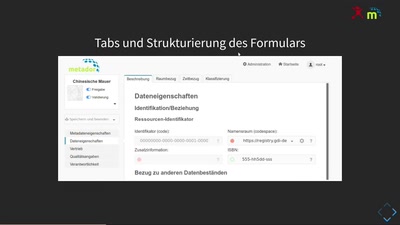
Make Metadata great again (nee, nur ein Witz. Kein…

30 min
Informationsfreiheit trotz CSU
25 min
Konfomität, Anpassungen, CSW

37 min
Don't ask what you can do for TPMs, Ask what TPMs can do…
next