Search for "Murdoc"
45 min
Reverse-engineering currency detection systems

58 min
Tampering the Tamper-Proof
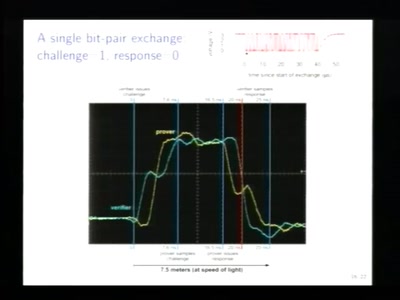
57 min
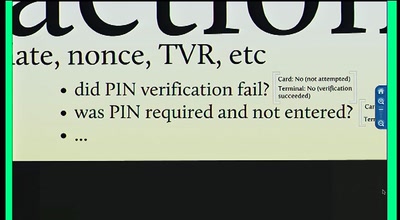
Vulnerabilities in the EMV Protocol
42 min
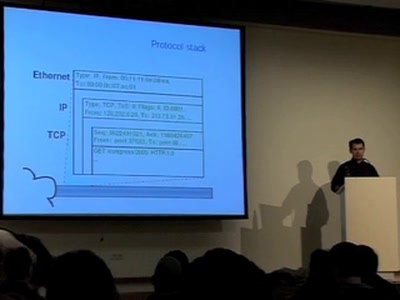
Creation and detection of IP steganography for covert…

62 min
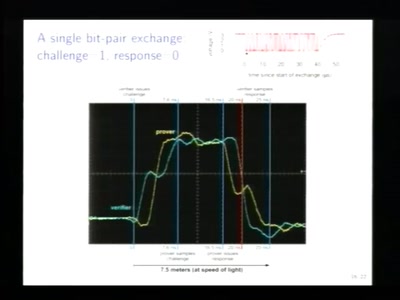
Hot or Not: Defeating anonymity by monitoring clock skew to…
62 min
Keeping your enemies close
60 min
Pleiten, Pech und Pannen in der Zahlungsdiensteregulierung
44 min
Tech unexeptionalism and the monopolization of every…

62 min
The surveillance state & modern day COINTELPRO tactics
63 min
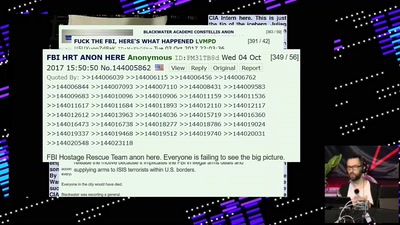
Eine kurze Geschichte von Q als Mindfuck-Spiel
59 min
Exposing the global banking watchlist