Search for "Ilja"
next
46 min
Look what I found under the carpet
107 min
Breaking software in an automated fashion
58 min
A survey of BSD kernel vulnerabilities.
73 min
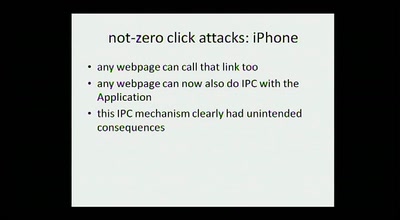
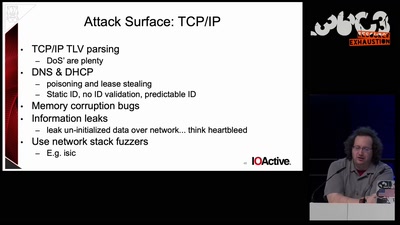
expanding the attack surface and then some
61 min
why clearing memory is hard.
51 min
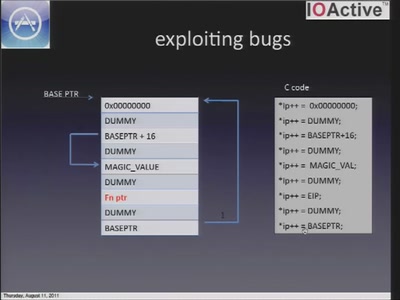
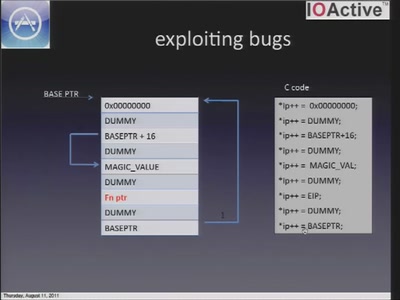
A look at the security of 3rd party iOS applications
51 min
Is it possible? 10 years experience from the first man who…
62 min
Auditing Boot Loaders by Example
43 min
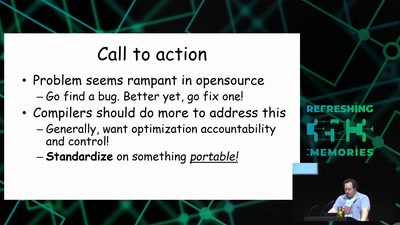
now is the time to take action!
next