Search for "various"
prev
next
57 min
a history of creative x86 virtual memory uses

20 min
Unleashing Reinforcement Learning in Penetration Testing…
46 min
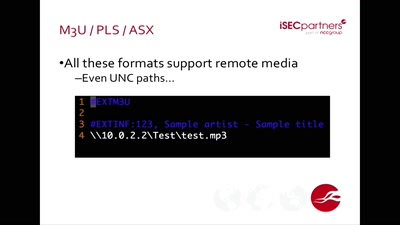
Is Your Document Telling on You?
39 min
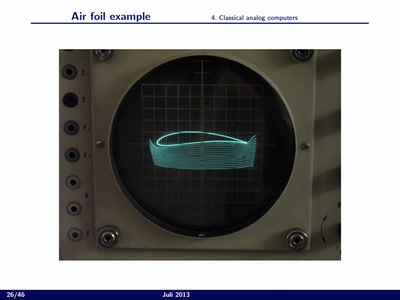
High performance/low power computing based on the analog…
67 min
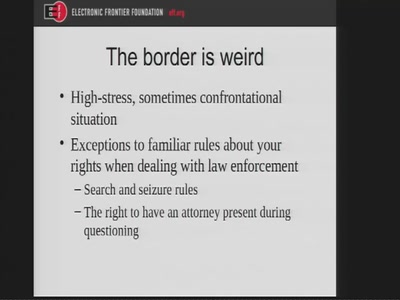
A Privacy Guide for Travelers
45 min
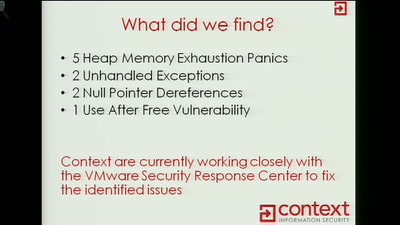
Exploiting VMWARE ESXi Binary Protocols Using CANAPE
60 min
getting out of surveillance state mode
57 min
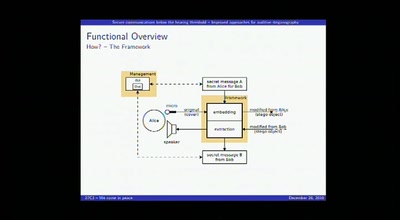
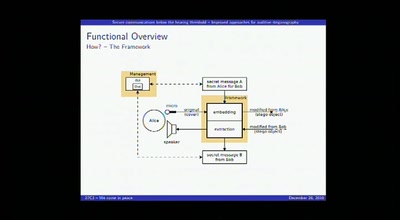
Improved approaches for auditive steganography
43 min
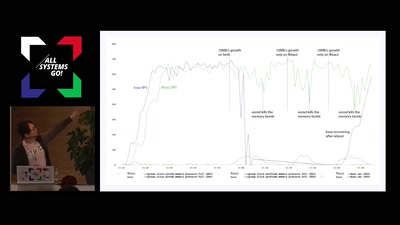
Functional resource control using cgroup2

55 min
Implementation, hazards and updates on use of RNGs in…
prev
next