53 min
Teach yourself upper management in 22 days

93 min
A roundup and live demonstrations of all currently known…
52 min
Wireless connections of 20km and more

55 min
The "anyOS" paradigm and its implications through…

64 min
A major new version of freenet
53 min
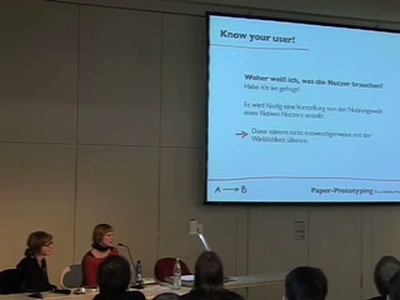
Erfahrungen aus der Praxis
57 min
Why developing Secure Software is like playing Marble…
44 min
What the heck is realtime - and what to do with it

64 min
Oder: worüber wir nächstes Jahr lachen werden
51 min
Elevated to the Next Level
56 min
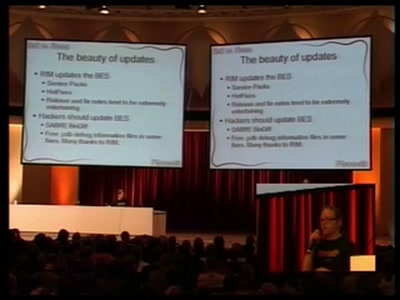
Reverse Engineering the Motorola EZX (A768,A780,E680)…

66 min
Learn how to effectively protect not only your data but…
113 min
17 Mistakes Microsoft Made in the Xbox Security System &…
51 min
How to build your own radar system
53 min
Satellite Tracking, harvesting and security
53 min
How to find any book (and many other roadkills) on the…

46 min
Chasing hackers with a bunch of monkeys
107 min
Breaking software in an automated fashion
46 min
Was ist denn nun eigentlich so ein 'Interrupt'?
54 min
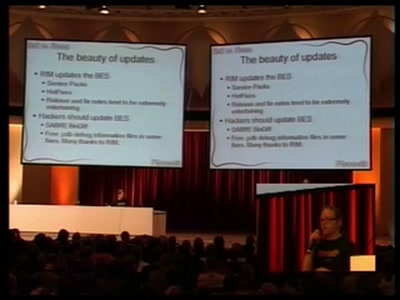
Consequences of Spam and Virus Filtering for the E-Mail…

52 min
Scanning your GPRS/UMTS IP network for fun and profit

52 min
A lamer's introduction to retrieving "sensitive"…

61 min
Everything you need to know about Podcasting
54 min
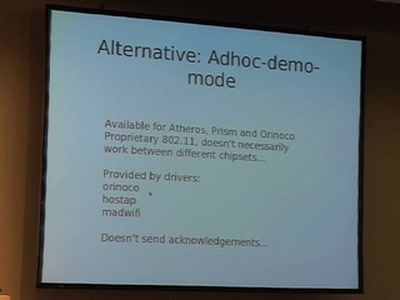
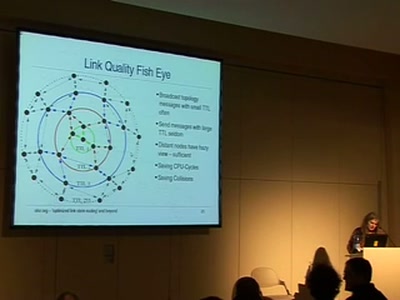
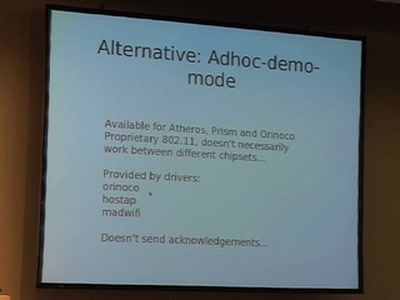
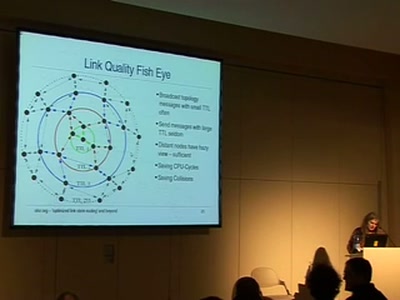
Ubiquitous wireless mesh clouds with olsrd from olsr.org

38 min
Presentation of an innovative buffer overflow uncovering…

61 min
Language/VM R&D, whole program type inference, translation…

43 min
An open-source project to develop a tool for broadband…
64 min
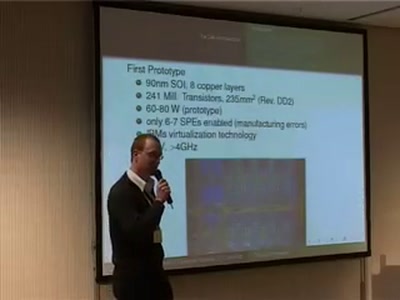
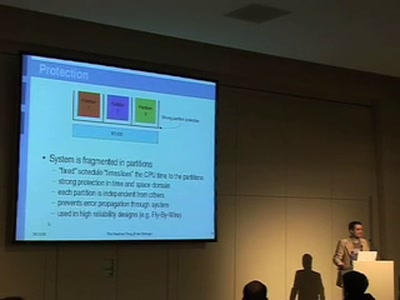
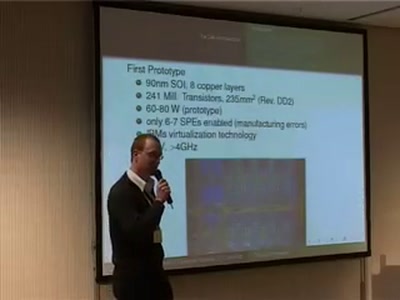
Computing of Tomorrow or Yesterday
49 min
Old Laws and New Technology the German Way
56 min
Profiling Modern Espionage
50 min
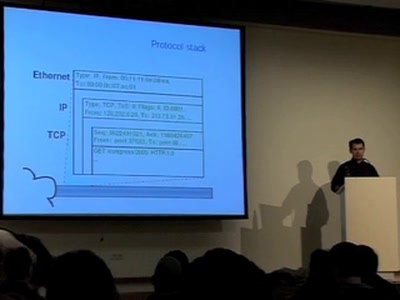
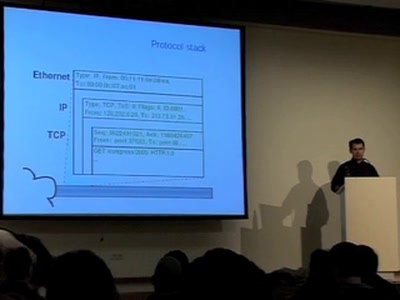
Writing your own flexible Userland TCP/IP Stack - Ninja…

49 min
MMIrDA - Major Malfunction's InfraRed Discovery Application

60 min
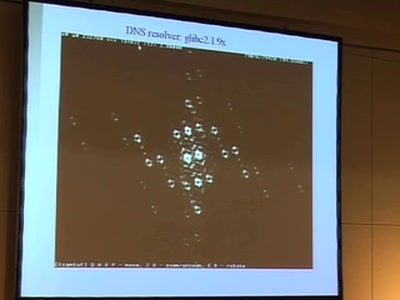
New Explorations: Large Graphs, Larger Threats

49 min
How bureaucrats fail to fight terror
45 min
On automated video analysis of human behaviour
56 min
Watching the watchers, having fun with cctv cameras, making…

47 min
An in-depth look at p2p algorithmics

45 min
An overview of static and dynamic approaches

52 min
Reverse-Engineering des Embedded-Linux-Navigationssystems
47 min
ISO14443, ISO15693, their GPL librfid implementation and…

49 min
Introduction to SIP Hacking
59 min
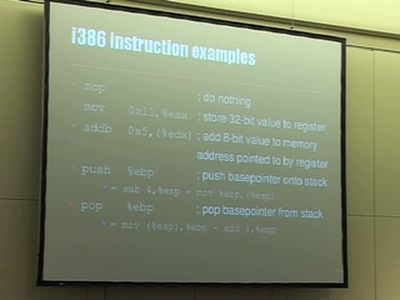
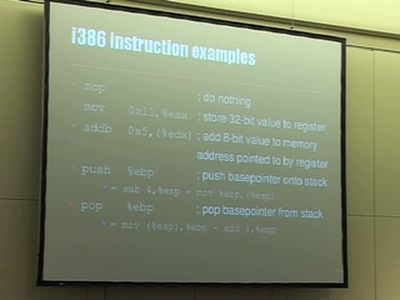
The fascinating interplay of CPU, stack, C-compiler and…
59 min
Fast development of object-oriented functional programs
42 min
Creation and detection of IP steganography for covert…

49 min
Introduction to syscall proxying and applications for in…
![Advanced Buffer Overflow Methods [or] Smack the Stack](https://static.media.ccc.de/media/congress/2005/22C3-491-en-advanced_buffer_overflow_methods.jpg)